Lots of organizations, unfortunately, do not fully understand what SIEM is. There is a basic idea behind most SIEM systems. They centralize network activity in a format that is easier to digest. But for a particular organization, the method of using SIEM will depend on the goals. However, there is a selection of popular options for using such systems. More than this, an expert siem service provider can help you choose the right variant.
The principle of operation of SIEM systems
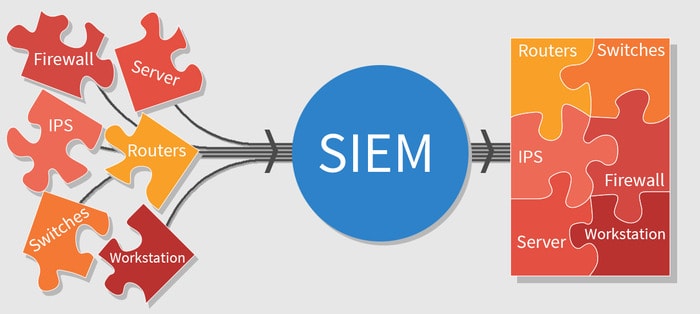
The concept of SIEM (Security Information and Event Management) is quite vague these days, and one can imagine that it is a process that combines network activity into a single address data set. The term itself was coined by Gartner in 2005, but since then the concept itself and everything related to it has undergone many changes.
Initially, the abbreviation was a combination of two terms denoting the scope of the software:
- SIM (Security Information Management) – information security management;
- SEM (Security Event Management) – security event management.
According to Gartner, a SIEM system must collect, analyze, and present information from network and security devices. It should also include identity and access management applications, vulnerability management tools, and databases and applications.
For clarity, we will highlight a few features that are usually supplied by SIEM systems:
- Ability to send alerts based on predefined settings.
- Reporting and logging to simplify auditing.
If you think this is like a tampering detection system, you are right. SIEM collects logs of various applications, processes them, and puts them in centralized storage that is convenient to work with.
More than this, auto-location, as well as periodic updating of sources, experts attribute to the advantages. However, there is no consensus on the issue of updating a SIEM solution. The lack of auto-updating of analyzers is sometimes explained by vendors as protection against changes in the analysis logic, and they offer to carry out SIEM changes under the supervision of their own specialists. This approach increases the cost of ownership of the system, as UnderDefense explains.
SIEM systems for daily business challenges
When choosing a SIEM solution, it is worth considering not only the cost of licenses but also TCO. The larger the organization, the more network events occur in its IT infrastructure. Both external and internal. And there are more and more threats. In order to control a huge amount of data and not miss a security threat to business-critical information, it is necessary to implement complex end-to-end security event tracking systems.
For example, in order not only to respond quickly to threats but also to be able to prevent them in the future, a security specialist (we are talking about large companies that can afford it) must receive information about all events in its IT infrastructure in an understandable way.
Any networking event can be called a security event (for example, an email exchange, identification in an enterprise CRM system, or a request for access to any information under conditions) when this event indicates a possible violation of the information security policy or the occurrence of a previously unknown situation related to security. To collect and analyze this kind of information, you can get the help of UnderDefense specialists.
How to choose the right SIEM solution
SIEM systems differ in structure, scalability, functional properties, and the number of tasks to be solved. Product evaluation should be based on several important basic characteristics.

Here are some SIEM systems features listed:
- Event sources and handling. The more event sources a system supports, the more effective the protection. At the same time, the solution must provide an individual approach to the normalization of each event from various sources. Working with the program facilitates the breakdown of events into categories. Syntactic analysis of information flows (parsing) of such solutions is implemented by designating the most critical fields. Parsers are updated, as a rule, simultaneously with the introduction of additions or changes to the system.
- Collection of incidents An effective SIEM is a platform with the functions of normalizing, combining, and filtering incidents. The advantage will be the processing and storage of raw events. The speed of the processes does not affect the overall picture. Masking information and monitoring network traffic are auxiliary functions but not useless. It is possible to check the correct operation of normalization, filtering, and aggregation at the stage of testing SIEM in combat mode. Therefore, manufacturers who provide a free test drive of a fully functional version of the product are more trustworthy.
- Correlation. The optimal SIEM solution compares events in real-time, is able to conduct behavioral analysis, and compares historical data. Flexible settings of the correlation system, enrichment of incidents in the connector or the management console, an additional function in the form of a manual check, and the ability to work with all mechanisms simultaneously are the hallmarks of a good SIEM.
- Visualization. Reporting of SIEM systems is most often formed in the form of graphs, histograms, and tables. Most reports are exported to five file formats: MS Excel, RTF, PDF, CSV, and HTML.
- General settings and built-in functionality. The convenience of working with SIEM depends, first of all, on the presence of built-in event correlation conditions, graphical panels, and report templates. The more built-in correlation resources, the less qualified, and therefore paid, assistance from third-party specialists will be required when servicing the platform. An important marker of the convenience of working with SIEM is the ability to centrally coordinate platform components from a single console, as well as automatically update pre-installed policies and reporting templates. All this will facilitate the work of a specialist.
Conclusion
It is recommended to choose a solution that interacts with the maximum number of heterogeneous systems that are used in the company. A multi-layered incident processing platform will speed up work with sources and easily adapt to the software. Low requirements for hardware and software will be an additional advantage.
As well, when choosing a SIEM solution, it makes sense to take into account not only its cost of licenses and technical characteristics but also consider its provider.