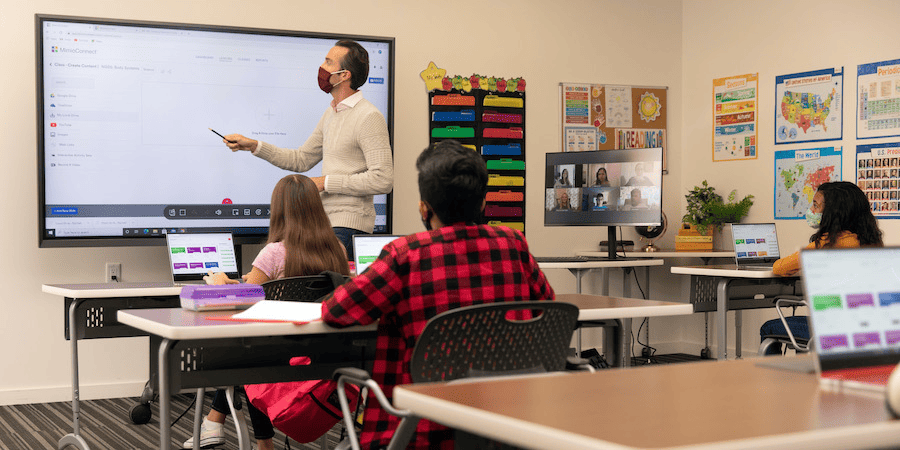
Modern classrooms are rapidly changing. Textbooks are being replaced by portable devices that provide relevant and updated instructional materials in real-time. Exams that used to be conducted in print and paper are transitioning into digital assessments. Multiple educational institutes have wholeheartedly embraced trends like One-Device-Per-Student (1:1) and Bring-Your-Own-Device (BYOD) to create personalized and far more engaging learning experiences for the increasingly tech-savvy learners of this century.
Technological resources are no doubt brought into classrooms by educators with the best of intentions. However, at times those also provide a quick route to multiple distractions for the learners. Placed in front of an open device with seamless internet access, students browse through social media sites, play video games or send online messages to peers. Consequently, distraction during ongoing lectures is inevitable and almost unavoidable unless access to the web is blocked. Such digital distractions not only affect the flow of teaching but can also interfere with the learning experience of students. Lack of concentration and reduced academic involvement are the challenges that teachers are often grappled with in a digital classroom.
Catering to a generation of digital natives, teachers need to utilize a broad spectrum of classroom management tools and methods to effectively deal with such technology-driven distractions. This can also empower them to prepare a learning environment that is interactive, visually rich, and can enable learners to optimize their potential for future success.
Importance of Classroom Management Tools in Digital Classrooms
To support a technology-enabled education system, teachers need to combine their traditional classroom management methods with digital tools. Educators need to understand that digital devices are undoubtedly appealing and interesting to divert young minds. Hence, educators need to move towards student-led discussions and interactions that can provide learners with creative autonomy. If encouraged to dig down deeper to learn fresh concepts, there is a higher possibility that learners will focus on leveraging technology as an integral part of their learning process rather than a means of entertainment.
Adopting such a blended approach to classroom management can aid teachers in devising interactive and engaging instructional methods that may require students to collaborate with each other and learn through an inquiry-based approach. For example, a system for learning management can be an excellent classroom tool to promote academic learning. It usually has features that allow students to attend educational courses through the platform. It also allows them to access certain instructional materials, which can help facilitate efficient learning.
Indeed, by integrating technological tools in their classroom management principles, educators can set expectations for specific projects and track the academic progress of students in real time. They can thus create a task-oriented, independent, and engaging learning environment that can effectively cater to the diverse learning patterns and styles of young brains.
How Classroom Management Technology Can Empower Teachers to Enhance Learning

For effective classroom management, teachers need to be constantly aware of student activities during an ongoing lecture. Effective monitoring tools can help teachers keep track of student activities from a single interface and control them per the lesson requirements. Such kind of visibility also allows teachers to find individualized solutions toward digital distractions and make more optimized usage of the classroom time.
Multiple classroom management tools allow teachers to gain remote access to student devices, which can be helpful in redirecting students using technology incorrectly or helping them navigate through the required material for the next classroom activity. Some classroom management solutions also allow teachers to provide a hands-on learning experience, by allowing them to broadcast their own device screen or a student screen to the rest of the class. This enables them to promote a peer-based learning model and maximize student engagement in the class.
Effective classroom management tools can also enable teachers to connect with learners in groups or one-on-one to deliver personalized instruction per the learning needs of students. Teachers can provide immediate assistance to specific students via the private chatting feature and help them with their queries without disrupting the rest of the class. Teachers can also categorize students into teams and assign a specific set of tasks to them. With the help of the group chatting feature, teachers can encourage student-led activities and brainstorming sessions in which students can engage in self-directed learning. With groups of learners assigned to specific project work, educators can easily pace up with the lesson.
With the aid of appropriate tools, teachers can also conduct quick quizzes and tests that can help them to retain student focus on the lessons concerned and improve the learning outcomes. Educators can also conduct assessments in a highly secure environment and provide immediate feedback via an electronic grading system.
With all these things being said, there’s no question how important classroom management software is for academic institutions, educators, and students. But with various options to choose from, finding the right classroom tool can be a bit challenging. There are some considerations to take to ensure educators pick the appropriate system for their needs. For example, educators want their software to be less daunting or time-consuming to set up. They’re also looking for one that offers straightforward implementation and maintenance.
Moreover, it’s essential for educators to feel comfortable about adopting certain classroom management software to ensure more desirable student learning outcomes. Lastly, academic institutions and educators should consider choosing a solution that promotes student engagement. This means that the software they should choose has features that can help teachers encourage student participation and collaboration. These features may include messaging, the ability to share screens, and other solutions that enable educators to give real-time feedback.
Benefits of Non-Restrictive Restoring Remediation Measures in Education
In a digitized classroom, workstations need to be maintained at their highest functional level so that students can access them anytime as per their diverse learning requirements. However, technical difficulties arising out of issues, such as accidental configuration drifts and unauthorized software installation, can cause extended downtime and interrupt the seamless flow of teaching and learning. In an attempt to find a better alternative to constantly re-imaging damaged machines, system administrators take recourse to restrict students’ ability to access the device. However, this approach severely curtails students’ freedom to learn through an experimental approach and can have a negative impact on their academic achievement.
Restorative remediation measures based on reboot to restore technology can provide an effective solution to this problem by allowing the support team to mark the desired state of baseline configuration in classroom workstations. Its non-restrictive power allows the students to make any system changes and learn in a free and open learning environment. However, all such user inputs, unauthorized or malicious, are completely removed from the devices by the reboot to restore solutions, and the admin-determined baseline is restored. Moreover, this simple-yet-powerful system restoration mechanism can be enabled with a system restart. This enables teachers to fix system issues themselves, thus reducing downtime and dependency on manual IT intervention.
When such reboot to restore-based remediation principles is in place, students can be given complete access to the classroom devices without management restrictions, which enhances their classroom technology experience. Teachers can conduct lessons in a uniform and consistent environment, thus leading to more effective and result-driven classroom management.
Conclusion
Effective classroom management strategies coupled with the usage of the right digital tools can help teachers gain technical control, maximize system availability, and introduce various ways of learning innovation that ensures smooth continuity of the lesson and higher student engagement.
With the information mentioned above, educators will know and understand the importance of classroom management software in digitized learning environments.